Protect Your linkedin hacked account: Recovery Guide for 2026

That gut feeling that something’s wrong with your LinkedIn account? Trust it. It's often the first and best sign that you need to take a closer look.
Most people assume a hacked account means bizarre posts start showing up on their feed. In reality, the initial red flags are usually much more subtle, hiding in plain sight within your profile's activity logs and settings. Spotting these signs early can be the difference between a quick password reset and a full-blown professional crisis, especially if your reputation and client relationships are on the line.
How to Spot a Hacked LinkedIn Account Early
Before a compromise turns into a disaster, you need to know exactly what to look for. Hackers are banking on you not noticing the small, quiet changes they make.
Unusual Profile Modifications
The first place to check is your own profile. Attackers often tweak small details, hoping they'll fly under the radar.
Be on the lookout for any of these changes:
- Your Job Title or Company is Different: A hacker might change your current role to promote a scam or spread bad information.
- Your Summary or Headline is Rewritten: Your professional bio could be edited to include malicious links or strange, out-of-character messaging.
- New Profile Picture or Banner: An unexpected change to your main profile images is a dead giveaway that someone else has access.
- Weird Skill Endorsements: Suddenly getting endorsements for skills you don't have from people you don't know? This can be a sign of bot activity or that a compromised account is being used to legitimize other fake profiles.
Strange Network and Messaging Activity
Beyond your profile page, the real damage often happens in your DMs and connection requests. A compromised account is a powerful tool for scammers because it uses your credibility to fool your network.
Keep a close watch on these areas:
- New Connections You Didn't Request: If you see new people in your network that you never sent a request to, that’s a huge red flag.
- Sent Messages You Didn't Write: Always scan your "Sent" folder. Hackers love using a trusted account to send phishing links to your connections. This is one of the most common signs of a linkedin hacked account.
- Withdrawn Job Applications: For those on the job hunt, an attacker might withdraw your applications just to cause chaos or sabotage your efforts.
To help you prioritize, here’s a quick way to gauge the severity of different warning signs.
Hacked Account Warning Signs Severity Matrix
This matrix can help you quickly assess the risk level of different suspicious activities and decide how fast you need to act.
| Warning Sign | Risk Level | Immediate Action Recommended |
|---|---|---|
| Endorsements from strangers | Low | Monitor account activity closely. |
| New, unrecognized connections | Medium | Review active sessions and change password. |
| Unauthorized profile changes | High | Immediately change password and enable 2FA. |
| Messages you didn't send | Critical | Force sign-out of all sessions and contact support. |
| New sign-in security alert | Critical | Instantly end the unrecognized session and lock account. |
If you see anything in the "High" or "Critical" categories, don't wait. The faster you respond, the less damage can be done.
Expert Insight: A hacked account isn't just about what's posted publicly. The real danger lies in the background—in your private messages and connection requests, where hackers exploit your professional reputation to scam others.
Alarming Security Alerts
LinkedIn has built-in security features that act as your digital tripwires. You should never, ever ignore them.
The most important one is the email alert about a new sign-in from a device or location you don’t recognize. If you’re in Chicago and get an alert about a login from halfway across the world, it’s time to act immediately.
You can check this yourself by going to Settings & Privacy > Sign in & security > Where you're signed in. This page lists every single device logged into your account. If you see one that isn't yours, you can end that session instantly. To get a better handle on this, understanding your LinkedIn account activity history is the key to spotting anything out of the ordinary.
Remember, the threat is real and growing. In late 2025, a massive data exposure of 4.3 billion professional records put a spotlight on just how vulnerable this information is. With names, job titles, and contact details out in the open, hackers had everything they needed to start taking over accounts. You can read more about how this data leak impacts account security and see why staying vigilant is non-negotiable.
When you realize your LinkedIn account has been hacked, that gut-sinking feeling is followed by a rush of panic. You have to act fast. Every minute a hacker has control is another minute they can damage your reputation or exploit your network. This isn't about overthinking; it's about taking swift, methodical action to lock them out.
First things first, try to reclaim your account, even if you think you're already locked out. Go directly to LinkedIn's password reset page. Even if the hacker has changed your password and primary email, this kicks off a security process. LinkedIn will fire off a reset link to all email addresses tied to your account, which could be the lifeline you need to get back in before they sever all your recovery options.
This quick process flow shows you how to size up the situation from the get-go.
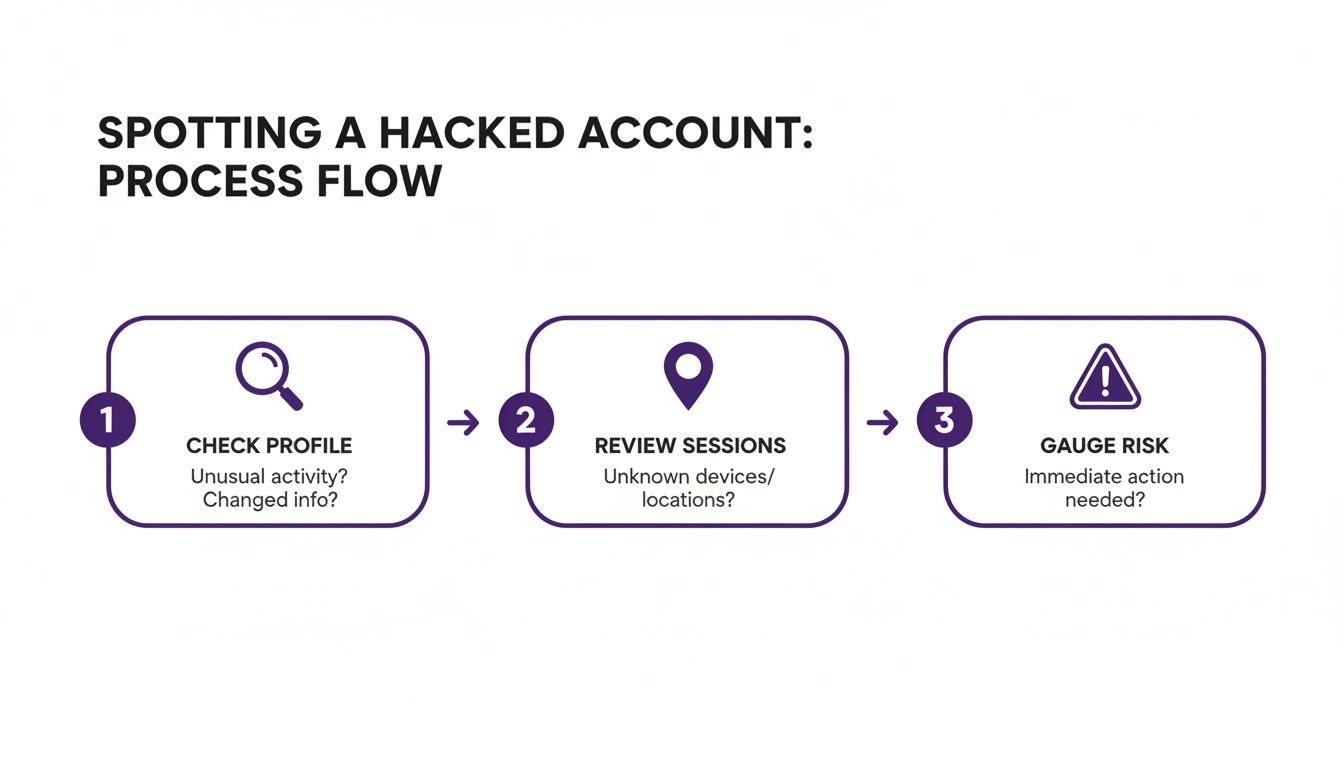
Think of it as triage: check for unauthorized profile changes, review your active sessions for anything that looks off, and get a sense of the damage so you know what to do next.
Forcibly End All Active Sessions
If you manage to get back into your account, your immediate priority is to give the intruder the boot. The quickest way to do this is by forcing a sign-out on every single device.
Head to Settings & Privacy > Sign in & security > Where you're signed in. This page is your security dashboard, showing you every active login—device, location, and all. Don't waste time trying to figure out which session is the hacker's. Just hit "Sign out of all sessions." This is the big red button that logs everyone out, everywhere.
Key Takeaway: Forcing a universal sign-out is your digital panic button. It’s the fastest way to sever an attacker's connection and buy yourself the time you desperately need to change your credentials and lock things down.
Once you've done that, you have a clean slate. Immediately change your password to something long, complex, and brand new—nothing you've ever used before.
Disconnect Suspicious Third-Party Apps
Hackers don't always come through the front door. Sometimes, they sneak in through a third-party app you connected ages ago and forgot about. These apps can be a persistent backdoor right into your account.
It’s time to seal it shut.
- Navigate to
Settings & Privacy > Data privacy > Other applications. - You'll see a "Permitted services" tab. This lists every external service with access to your LinkedIn profile.
- Scan this list carefully. If you see anything you don't recognize or no longer use, click "Remove" immediately.
This revokes the app's permission to access your data or post on your behalf. It’s a critical cleanup step that’s easy to overlook in the heat of the moment.
Halt All Your Outreach and Automation
If you're in sales or recruiting, a hacked account is a nightmare scenario. Your powerful outreach tools can be turned against you in an instant.
Just think about it: a hacker with access to an account connected to Expandi or Waalaxy could hijack your live campaigns. They could start blasting malicious links or scam messages to your entire pipeline of prospects and clients. The reputational damage would be immense.
You need an emergency shutdown protocol for your tools.
- Pause Everything: Log into your automation tool's dashboard and stop every single active campaign. Don't just pause—stop them.
- Check API Keys: If your tool connects via an API key, revoke it. You can generate a new one later, once your account is 100% secure.
- Audit Your Tools: Check the access logs inside your automation platform. See if there's any unusual activity that originated from there.
Taking your outreach tools offline cuts off a major attack vector and protects your professional relationships. Don't even think about turning them back on until you are absolutely certain your LinkedIn account is secure.
Navigating the Official LinkedIn Account Recovery Process
When you realize you're locked out of a hacked LinkedIn account, the official recovery process can feel like a maze. The first thing you need to do is find LinkedIn's identity verification page. Just search for "LinkedIn report hacked account," and you'll typically land right on their specialized support portal.
This isn't the time to be vague. When you start filling out their support form, you have to be crystal clear. State outright that your account has been compromised and you can’t get in.
Submitting Your Initial Recovery Request
Think of this first form as your opening statement to LinkedIn's support team. Your goal is to give them everything they need to start working on your case immediately, leaving no room for confusion.
Treat it like you're filing an official report—just the facts. You’ll need to provide the primary email and phone number that were originally on the account, even if you know the hacker has already changed them. Crucially, grab the URL of your LinkedIn profile. It's the one unique thing that will help support find your account instantly.
In the description box, give a quick, clear summary of what happened.
- Point out any red flags you saw. Something like, "I got a password reset email I never asked for," or "My team told me they were getting weird messages from my account."
- Pinpoint the date you lost access. This gives the support team a clear timeline to work with.
- Be explicit about your situation. Simply state, "I can no longer log in, and I believe the email and password have been changed."
This direct, fact-based approach helps get your case into the right hands much faster. Skip the emotional frustration and stick to the essential details of the breach.
Pro Tip: Before you hit submit, take a screenshot of the entire form. It’s a simple way to keep a personal record of exactly what you sent and when you sent it.
The Identity Verification Hurdle
After you send your request, brace yourself for the next step: LinkedIn will almost certainly ask you to prove you are who you say you are. This is the most critical part of getting your linkedin hacked account back. They have to be 100% sure they’re giving access back to you and not the person who stole it.
This usually means you'll need to submit a clear copy of a government-issued photo ID, like a driver's license, passport, or national ID card. The name and photo on your ID have to be a match for what's on your LinkedIn profile.
To make sure this part goes off without a hitch:
- Use a high-quality image. Take a clear, well-lit photo of your ID. Make sure all four corners are in the shot and that there’s no glare covering up your picture or any of the text.
- Send the right file type. LinkedIn typically asks for standard formats like JPEG or PNG.
- Follow their instructions to the letter. If they ask for the front and back, send both. If they want a specific angle, do your best to get it right.
It’s completely understandable to feel a bit uneasy about uploading a copy of your ID. But this is a standard security measure designed to protect your professional identity from being hijacked for good. To get a better handle on this, you can learn more about the account verification process in our detailed guide.
Post-Recovery Security Checklist
Getting access back from LinkedIn Support is a huge relief, but you're not done yet. The moment you're back in, you need to lock that account down to prevent a repeat performance.
The very first thing you should do is create a new, truly secure password. We're talking a long, random mix of uppercase letters, lowercase letters, numbers, and symbols. Most importantly, it has to be a password you've never used anywhere else.
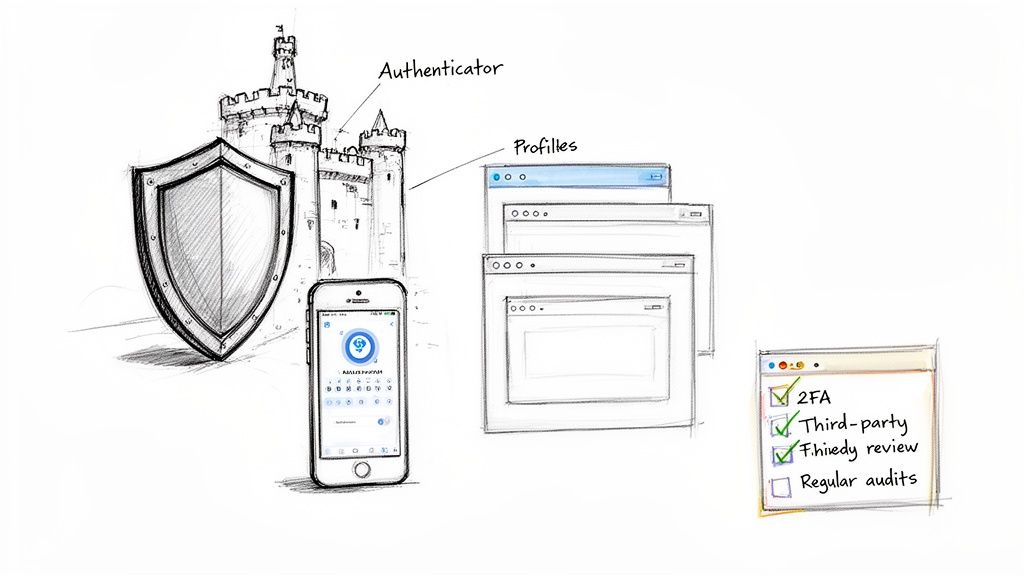
Immediately after that, turn on two-factor authentication (2FA). This is probably the single best thing you can do to secure your account. Skip the SMS option and use an authenticator app like Google Authenticator or Authy—it's far more secure.
Here’s your immediate to-do list once you're back in control:
- Set a Strong, Unique Password: Use a password manager to generate and save a complex password that no one could ever guess.
- Enable 2FA with an Authenticator App: This forces any login attempt to be verified with a time-sensitive code from your phone, stopping hackers in their tracks.
- Review and Update Your Primary Email: Make sure the email tied to your LinkedIn is secure. Go change that password too and switch on 2FA there as well.
- Check for New Secondary Emails or Phone Numbers: Hackers love to add their own contact info as a backdoor. Dig into your settings and delete any emails or phone numbers you don't recognize.
Running through these steps slams the door shut on the hacker and gives your account a much-needed security upgrade, turning a nightmare scenario into a powerful lesson.
How to Repair Your Professional Reputation After a Hack
Getting back into your hacked LinkedIn account is a huge relief, but don't celebrate just yet. The next few hours are critical for managing your professional reputation. How you handle the cleanup and communication will determine whether your network’s trust is restored or permanently damaged.
Your connections, clients, and prospects need to hear from the real you, and they need to know what happened. Right now, transparency is your best friend. A vague or delayed response lets suspicion grow, but a clear, honest message shows you’re back in control.
Crafting Your Public Announcement
The very first thing you should do is post an update on your LinkedIn feed. This addresses everyone at once and creates an official record that you've secured your account.
Keep the message direct and professional. You don’t need to get into the weeds about the technical details of the hack; just cover the essentials.
Here’s a solid approach for your post:
- Acknowledge the breach: State clearly that your account was compromised but is now secure.
- Warn your network: Advise people to ignore any strange messages or connection requests sent from your account within a specific timeframe.
- Apologize for the hassle: A quick apology shows you understand the confusion it may have caused.
- Reassure them: End on a positive note, confirming you're back in control.
This isn’t just about damage control. It's about showing integrity. Being upfront can turn a negative incident into a moment that actually reinforces your professionalism.
Auditing Your Account for Malicious Activity
Before moving on, you have to play detective. You need to do a full sweep of your account to figure out exactly what the hacker did. This means digging into your activity to find and reverse any damage.
Your main focus should be sent messages and connection requests. Go through your direct messages with a fine-tooth comb, looking for any conversations you didn’t start. You’re hunting for phishing links, scammy offers, or any other bizarre messages sent to your contacts.
When you find a malicious message, you can often delete or retract it. Doing so can pull it from your contact's inbox, cleaning up the mess before they even see it. At the same time, check your sent connection requests and withdraw any you don't recognize.
Key Takeaway: A detailed audit isn't optional. You must know what was sent from your account to effectively clean up the damage and protect your network from further harm. This proactive step helps rebuild trust faster.
Handling Direct Outreach to Affected Contacts
For anyone in B2B, the stakes are much higher. If a hacker spammed a high-value client or a warm lead, a public post simply won't cut it. You need to reach out with a personal message, and fast.
Start by explaining the situation calmly. Apologize directly for the message they received and confirm it wasn’t from you. Reiterate that your account is now secure.
This direct, personal touch can surprisingly strengthen your professional relationships. It shows you value them enough to address the issue one-on-one, which reinforces their trust. This is particularly important given how common data breaches have become. The massive 2021 breach that exposed data from nearly 700 million LinkedIn users—about 92% of the user base—showed just how easily this information gets weaponized for phishing attacks.
For seriously complex situations, professional reputation repair services for individuals can offer expert help in navigating the fallout.
Playing the Long Game: How to Bulletproof Your LinkedIn Account
Getting your LinkedIn account back is a huge relief, but the work isn't over. Now comes the most important part: making sure it never happens again.
It's time to shift from frantic damage control to building a real defense. Your goal is to make your account so difficult to crack that hackers won't even bother trying. This goes way beyond just having a strong password; it's about creating layers of security and adopting smart habits for the long haul.
Switch to an Authenticator App—Seriously
If you only do one thing after reading this guide, make it this: set up two-factor authentication (2FA). But don't just stop at the default SMS text message option. It's better than nothing, but it's far from foolproof due to a nasty trick called "SIM swapping," where a hacker convinces your phone company to give them control of your number.
A much safer bet is a dedicated authenticator app.
- How They Work: Apps like Google Authenticator or Authy live on your phone and generate a fresh six-digit code every 30 seconds. Without physical access to your phone and that code, a hacker with your password is completely stuck.
- Why They’re Better: Because the code is created on your device, it never travels over the vulnerable cell network. This simple step closes the biggest loophole in SMS-based 2FA and makes your account exponentially safer.
The setup takes maybe five minutes, but it's the single most powerful move you can make to prevent another linkedin hacked account nightmare.
Develop Good Digital Hygiene
Strong security isn't a "set it and forget it" task. You have to maintain it, just like a car. A few simple, quarterly check-ups can stop major problems before they start.
First, get into the habit of checking the "Where you're signed in" page in your account settings. Scan the list for any weird devices or locations. See a login from a city you've never been to? End that session immediately.
Next, clean up your connected apps. Navigate to Settings & Privacy > Data privacy > Other applications and ruthlessly revoke access for any service you don't actively use anymore. Every connected app is another potential door into your account; the fewer doors, the better.
A Word From the Trenches: We see this all the time—hackers get in through slick phishing attacks. They'll send a fake DocuSign link through LinkedIn Messenger that looks completely legit. You click it, land on a pixel-perfect fake login page, enter your credentials, and it's game over.
Learn to Spot Sophisticated Phishing Attacks
Forget the old emails with bad grammar and spelling mistakes. Today's phishing is surgical. Scammers will use a compromised account to send targeted messages to that person's connections, abusing the built-in trust you have for a familiar face.
They'll send you a link to a "confidential project" or an "urgent invoice," which leads to a credential-stealing website. To build a strong defense, it's crucial to know how to protect personal information online. Be suspicious of every unexpected link, even if it seems to come from your boss. If a link asks you to log into Office 365 or Google just to view a document, stop. That’s a classic red flag.
Isolate Your Outreach with Proxies and Browser Profiles
For anyone running outreach—especially sales teams and agencies juggling multiple LinkedIn accounts—the stakes are way higher. One hacked account can paralyze your entire operation. This is where you need to get more advanced with dedicated proxies and browser profiles.
- Dedicated Proxies: A proxy gives each LinkedIn account its own unique IP address. This is critical for preventing LinkedIn from flagging multiple accounts running from the same office, which can lead to restrictions and make them more vulnerable.
- Browser Profiles: Tools like GoLogin or Multilogin let you create a completely separate and contained browser environment for each LinkedIn account. This sandboxing approach stops cookies and digital "fingerprints" from bleeding over, keeping each profile clean.
This setup does more than just keep your accounts stable. If one account does get compromised, the breach is completely isolated to that single browser profile. The rest of your assets are walled off and safe.
To really dig into these advanced techniques for scaling outreach safely, check out our full guide on LinkedIn account security. Adopting these strategies is how you turn your account's simple lock into a fortress.
Common Questions About Hacked LinkedIn Accounts
When your account gets compromised, your mind is probably racing with a million questions. Let's cut through the noise and tackle the most urgent ones we hear from people in your exact situation.
We’ll give you direct, no-fluff answers to help you figure out what to do next.
Will I Get My Account Back?
This is always the first question, and the short answer is: almost certainly, yes. But it’s going to take some patience.
LinkedIn has a specific recovery process for a linkedin hacked account, and it nearly always comes down to verifying your identity with a government-issued ID. As long as you can prove you’re the rightful owner, your odds are very high. The trick is to follow their instructions to the letter and get them everything they ask for right away.
Can Hackers Read My Old Messages?
Unfortunately, yes. The moment an attacker gets in, they have the same access you do. That means they can see your entire message history—every conversation, every attachment, every lead you've been nurturing.
This is exactly why you need to do a full audit of your inbox as soon as you regain control. You have to figure out what information they saw and which of your contacts they might have messaged with a scam of their own.
Important Takeaway: Work under the assumption that they've read everything. This will help you decide who you need to contact personally after securing your account, especially high-value clients who might have been part of sensitive conversations.
How Did My LinkedIn Account Get Hacked?
It’s almost never a case of someone guessing your password over and over. A hack is usually the result of a vulnerability somewhere else, and attackers have a few favorite methods.
Here’s what we see most often:
- Phishing Scams: You get a message that looks totally legitimate—maybe a link to a DocuSign or a shared file—but it takes you to a fake login page built to steal your credentials. These are getting incredibly common inside LinkedIn Messenger itself.
- Password Reuse: If you used your LinkedIn password on another site that got breached, hackers will take that leaked password and try it on your LinkedIn profile. It's a surprisingly common way in.
- Malware: Nasty software on your computer, like a keylogger, can silently record everything you type, including your LinkedIn username and password, and send it straight to an attacker.
Understanding how they got in is the first step to making sure it never happens again. The person who took over your account likely tricked you or exploited a weak link completely outside of LinkedIn’s control.
Should I Tell My Connections?
Absolutely, and you should do it immediately. Staying silent only makes things worse.
Posting a quick, professional message on your feed is the best move. It accomplishes three things at once: it informs your network, warns them to ignore any weird messages from "you," and shows everyone that you're on top of the situation. A little transparency here goes a long way in rebuilding trust after a security slip-up.
If you're running outreach with multiple accounts, a single hack can bring your whole operation to a standstill. BIDVA offers a solution: real, ID-verified, and fully warmed-up LinkedIn accounts. They give your team a secure foundation to scale campaigns without the constant risk. Protect your assets and keep your momentum by starting with profiles built to last.
Explore our secure accounts at https://buy-id-verified-account.com.

.png)